
Kubernetes Plugin Development and Security Monitoring
This article explores Kubernetes plugin development, security measures for Kubernetes and Docker, and network monitoring. It covers Kubernetes plugin management tool Krew, common commercial solutions, open-source Docker security tools, eBPF network monitoring, as well as related books and resources, serving as a comprehensive and practical technical guide.
1. Forms of Kubernetes Plugin Development
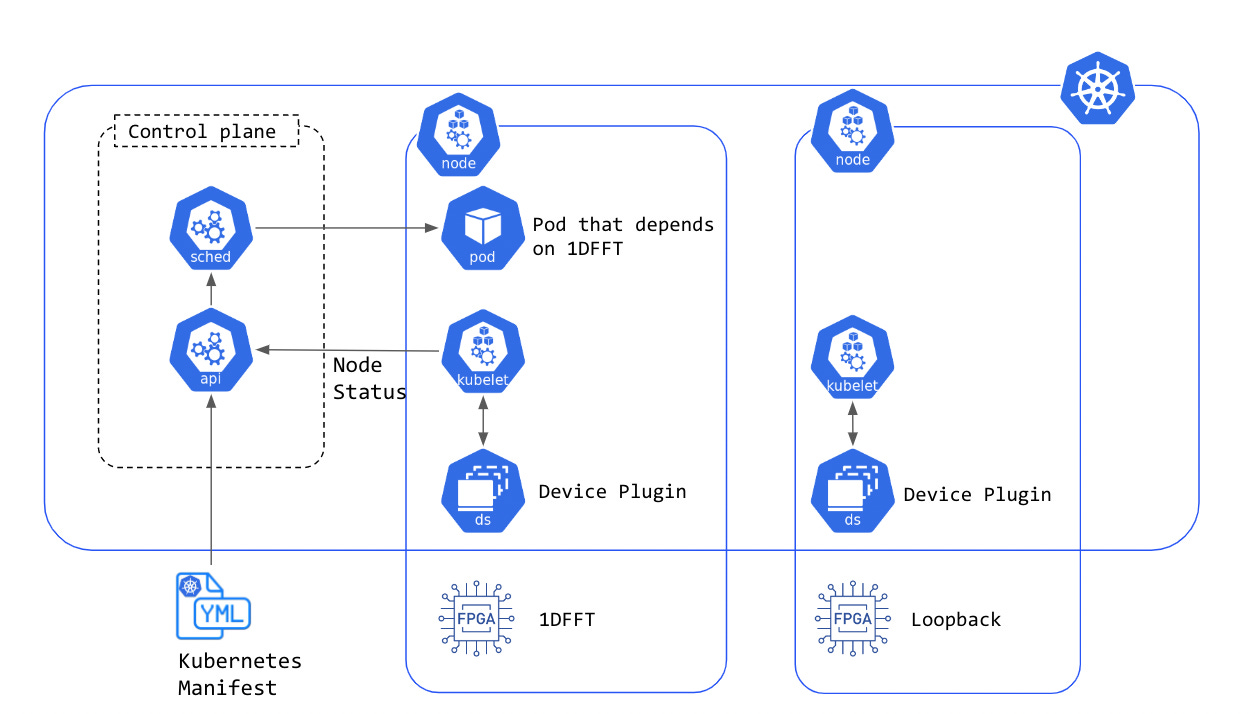
Kubernetes (K8s) is an open-source container orchestration platform widely used for managing and deploying containerized applications. To address diverse user needs, K8s supports various forms of plugin development.
1.1 Krew
Krew is a tool for managing, publishing, and searching kubectl plugins. With Krew, users can conveniently install and manage various plugins to enhance kubectl’s functionality.
- Features: Krew allows users to search and install various kubectl plugins, simplifying the installation and management process.
- Advantages: It provides a centralized plugin repository, ensuring plugin compatibility and quality.
- Usage: Users can easily install and use Krew plugins through the command-line tool.
For more information and plugin listings, visit the Krew official website. Refer to the Krew kubectl plugin development guide for guidance on developing Krew plugins.
1.2 Summary of Other Solutions
Apart from Krew, there are many other commercial and open-source solutions available. These solutions offer diverse features and services to meet various needs.
- Commercial Solutions: Calsoft provides professional Kubernetes plugin development services, assisting enterprises in customizing and integrating K8s plugins.
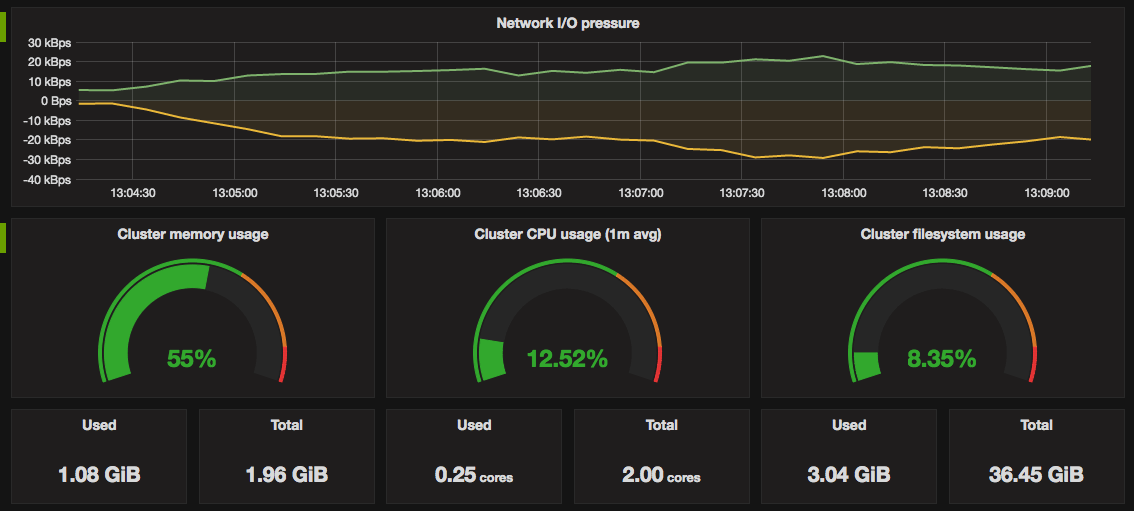
- Monitoring Tools: Various Kubernetes monitoring tools are available; see 13 common K8s monitoring tools. These tools help users monitor cluster performance in real-time, ensuring system stability.
2. Research on Open-Source Docker Security Measures
With the widespread use of Docker, container security issues have become increasingly important. This article discusses some open-source Docker security measures and tools.
- Docker Monitoring Blog Series: Link This blog series provides a comprehensive guide to Docker monitoring, covering various monitoring methods and tools.
- EBPF Container Monitoring Extension: Paper introduces how to use EBPF extensions for container monitoring.
- EBPF Container Monitoring Extension GitHub: Project Link provides open-source code and implementation details for EBPF extensions.
2.1 Security Issues with Docker
Docker’s security issues mainly focus on container isolation, network security, and permission management.
- YouTube Video Demo: Lockc – Container Security with EBPF LSM This video demonstrates how to enhance container security using EBPF and LSM.
2.2 Network Monitoring Research

Network monitoring is a crucial part of container security. By monitoring network traffic, security threats can be promptly identified and mitigated.
- cAdvisor Network Traffic Acquisition: Zhihu Article explains how to use cAdvisor to obtain network traffic data.
- Research on Network Topology Drawing: StackOverflow discusses methods and tools for drawing network topology structures.
3. Books Related to Kubernetes and Docker

Understanding theoretical knowledge and practical experience of Kubernetes and Docker is key to mastering these technologies. Here are some recommended books and resources.
3.1 Kubernetes Guide
- Kubernetes Guide provides a comprehensive guide to using Kubernetes, from basics to advanced applications, suitable for readers at all levels.
3.2 Container Security Resources
- Resource 1 and Resource 2 offer comprehensive information on container security, covering various security measures and best practices.
3.3 Kubernetes API
- Kubernetes API details the usage and practical experience of the K8s API.
3.4 Prometheus Overview
- Prometheus Overview introduces the principles and usage of the Prometheus monitoring system, essential for understanding and using Prometheus.
3.5 Docker Resource Compilation
- Compilation 1 and Compilation 2 provide rich Docker resources, including tutorials, tools, and sample code.
- Docker Networking Cookbook: Detailed guidance on configuring and managing Docker networking.
4. Mature Kubernetes Applications
- Grafana: Link Grafana is an open-source visualization tool widely used for monitoring and analyzing K8s cluster data.
- SegmentFault: Article offers in-depth discussions and practical experience regarding K8s and cloud resources.
- Syslog Free Trial: Link Syslog offers free monitoring and log management services, suitable for beginners and small teams.
5. Research on EBPF Implementation for Network Monitoring

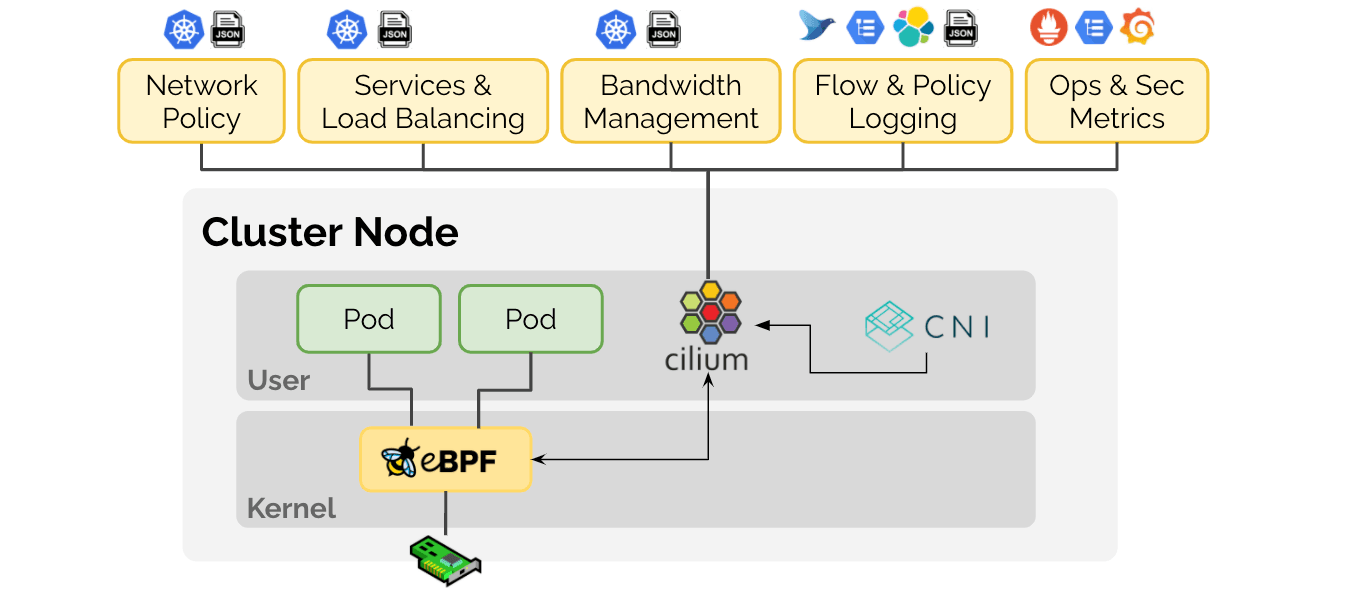
EBPF (Extended Berkeley Packet Filter) is a powerful tool for executing user-defined programs in the Linux kernel. It finds extensive applications in network monitoring and performance analysis.
- Isovalent Blog provides case studies and practical experience of EBPF in network monitoring.
- Sysdig is an EBPF-based monitoring tool that offers comprehensive system and network monitoring capabilities.
- Mizu Project: An open-source network monitoring project using EBPF technology for deep monitoring of container networks.
6. EBPF Security
The powerful capabilities of EBPF technology bring both convenience and security challenges. Here are some studies and practices related to EBPF security protection.
- Prevention and Monitoring of Malicious Use of EBPF: Meituan Technology Blog discusses how to detect and prevent malicious use of EBPF to ensure system security.
7. Docker Implementation Principles
Understanding Docker’s implementation principles helps in better utilizing and optimizing Docker. Here are some resources on Docker implementation principles.
7.1 cgroup Implementation Principles
cgroup (Control Group) is a Linux kernel feature used to limit, control, and isolate the resource usage of process groups.
- Analysis of cgroup Implementation: WeChat Article and Blog provide detailed analysis of cgroup implementation principles, helping readers understand the working mechanism of cgroup.
